Nude Photos Scandal Explodes In 520 Area Code – Full Video Exposed!
Have you heard about the shocking nude photos scandal that's rocking the 520 area code? What started as a quiet evening has turned into a massive privacy violation that's sending shockwaves through communities and raising serious questions about online security. This latest incident follows a disturbing pattern of intimate content leaks that have plagued the internet for years, but what makes this case particularly concerning is the geographic concentration and the sheer volume of content involved.
The Anatomy of a Digital Disaster
The internet exploded on August 31, 2014, when hackers released nearly 500 private photos of celebrities, marking one of the first major incidents that would change how we think about online privacy forever. What started as a quiet Sunday evening turned into one of the biggest privacy violations in Hollywood history. The scandal, nicknamed CelebGate or "The Fappening," would shake the entertainment industry and change how we think about online privacy forever.
This incident set a dangerous precedent that continues to haunt the digital landscape today. The ease with which intimate photos can be stolen, distributed, and consumed has created a thriving underground economy of stolen content. What's particularly troubling is how these incidents often target vulnerable individuals who never intended for their private moments to become public spectacle.
- Ice Spice Weight Loss Leaked The Forbidden Secret Thats Making Headlines
- One Day Well All Swear We Never Supported This The Shocking Leak
- You Wont Believe Belles Secret In This Leaked Disney Porn Clip
The Human Cost of Digital Exposure
The names and faces of sexual abuse victims become permanently etched into the internet's memory once leaked. Bank account and social security numbers in full view represent just the tip of the iceberg when it comes to the devastating consequences of these breaches. The psychological trauma, career damage, and personal relationships shattered by such violations cannot be overstated.
Recent incidents continue to demonstrate the ongoing nature of this problem. A series of unverified private videos allegedly involving Filipino actors Aaron Villaflor, Ron Angeles, Nikko Natividad, and Gil Cuerva have leaked online, triggering a fresh wave of online speculation. These young actors, whose careers were just taking off, now face an uncertain future as the scandal unfolds across social media platforms.
The Viral Nature of Scandal
The viral MMS video scandal, which gained significant traction on X (formerly Twitter) and Facebook during the final week of February 2026, have prompted legal experts to warn about the long-term consequences of sharing such content. Once intimate material enters the digital ecosystem, it becomes nearly impossible to completely remove. The speed at which content spreads across platforms means that by the time victims become aware of the breach, their private moments may have already been viewed by thousands or even millions of people.
- Shocking Alex Fines Nude Photo Leak Reveals His Secret Multi Million Dollar Fortune
- Mjr Cinema Waterford Michigan Leaked Nude Videos Shock Community
- The Godfather Coda 2020 Exposed Darkest Secrets And Shocking Leaks That Broke The Internet
This phenomenon isn't limited to celebrities or public figures. Ordinary people find themselves caught in the crosshairs of digital exploitation, often by people they know and trusted. The betrayal of trust can be as damaging as the public exposure itself.
Secret Networks of Exploitation
Police have uncovered a secret Facebook group where thousands of men, including husbands, were uploading intimate photos of women, often their own partners, without consent. The group, called "Mia Moglie (My Wife)," had been active since 2019 and grew to more than 32,000 members. This organized network of exploitation reveals how technology has enabled new forms of abuse that were previously impossible to coordinate at such scale.
The existence of such groups demonstrates that the problem goes beyond individual hackers or random leaks. There are organized communities dedicated to collecting and sharing non-consensual intimate imagery, creating marketplaces for stolen content that operate in the shadows of mainstream social media.
The Scale of the Problem
Search the world's information, including webpages, images, videos and more, and you'll find that Google has many special features to help you find exactly what you're looking for. However, this powerful search capability also means that once intimate content is uploaded, it can be indexed and made permanently available through search engines. The 80,000 nude files and $11.9 million extortion scandal (Rs 102 crore) according to the BBC, investigators believe Wilawan Eamsawat made about 385 million baht (Rs 102 crore) over the past three years, illustrates the massive financial incentives driving this illegal industry.
These staggering numbers reveal that intimate content leaks have evolved from isolated incidents into a sophisticated criminal enterprise. The financial rewards are so substantial that they attract organized crime operations willing to exploit technological vulnerabilities and human trust.
Political Figures and Public Trust
Anthony Weiner, Congressional portrait, c. 2007, Anthony Weiner is a former member of the United States House of Representatives from New York City who has been involved in multiple scandals related to sexting. The first scandal began when Weiner was a Democratic U.S. Representative. He used the social media website Twitter to send a link that contained a sexually suggestive picture of himself to a woman who was not his wife.
Weiner's case demonstrates how even powerful political figures can fall victim to the same temptations and vulnerabilities that affect ordinary people. His repeated involvement in sexting scandals ultimately destroyed his political career and personal life, serving as a cautionary tale about the permanent nature of digital communications.
The Digital Footprint Dilemma
Last time we checked, she had published 1,880 photos, 1,916 posts, and 78 videos. This level of digital activity represents the modern reality where our lives are documented and shared online at an unprecedented scale. The question becomes: how much of our private lives should we be willing to digitize, knowing that any of it could potentially be exposed to the world?
The answer varies from person to person, but the increasing frequency of leaks and hacks suggests that no one is truly safe from digital exposure. Even those who maintain minimal online presence can find themselves victims of breaches that expose information they never intended to share.
The NFL Connection
Girls fashion Sep 4, 2025 · Photos shockwaves through the NFL. 🏟️💣 Viewership explodes for Shedeur Sanders' debut, and the league is in full panic—they've been exposed. 😳🔥 The secret behind their declining ratings is finally out, and this unprecedented surge reveals a scandal so shocking it could shake the entire football world to its core—fans have spoken, and the.
While this particular scandal may seem unrelated to intimate content leaks, it demonstrates how quickly information can spread and how organizations struggle to control narratives once they escape official channels. The NFL's panic over viewership numbers and the alleged exposure of secrets mirrors the broader societal anxiety about loss of control over personal information.
The 2014 Watershed Moment
The 2014 celebrity nude photo leak represents a watershed moment in digital privacy history. From August 31, 2014, to October 27, 2014, a collection of nearly five hundred sexually explicit private photos and videos were posted online by an anonymous group that called themselves "Collectors." This coordinated attack on multiple high-profile individuals demonstrated the vulnerability of even the most secure digital storage systems.
The methods used in this breach—exploiting security questions, password resets, and iCloud vulnerabilities—highlighted how human factors often represent the weakest link in digital security. The victims were targeted not because of who they were, but because of what they represented: successful, attractive individuals whose private moments would generate maximum attention and traffic.
The Washington Football Team Fallout
Former cheerleaders of the Washington Football Team involved in the recent email scandal are dealing with emotional trauma over the situation. "They're all traumatized," Melanie Coburn, a former cheerleader, stated, capturing the human toll of these scandals. The email scandal revealed not just inappropriate content, but a culture of exploitation and abuse that had been hidden behind the glamour of professional sports.
This case demonstrates how intimate content scandals often reveal deeper systemic problems within organizations. The emails weren't just about individual misconduct; they exposed organizational cultures that enabled and normalized exploitation of women's bodies and labor.
Legal and Technological Responses
In response to the growing epidemic of intimate content leaks, lawmakers and technology companies have begun implementing new protections. Revenge porn laws have been enacted in many jurisdictions, making it illegal to distribute intimate images without consent. Technology companies have developed tools to help victims remove content and prevent its further distribution.
However, these measures often lag behind the technology used by perpetrators. The anonymous nature of many online platforms, combined with the ease of creating new accounts and sharing content across multiple sites, makes enforcement challenging. Victims often find themselves in a game of digital whack-a-mole, trying to remove content that keeps reappearing on new platforms.
Prevention and Protection Strategies
For individuals concerned about becoming victims of intimate content leaks, several strategies can help reduce risk. Using strong, unique passwords for all accounts and enabling two-factor authentication provides a crucial first line of defense. Being cautious about what intimate content is created and stored digitally, and using encrypted storage solutions for sensitive materials, can limit exposure if a breach occurs.
Education about phishing attempts, social engineering tactics, and the importance of regular software updates can help individuals recognize and avoid common attack vectors. Understanding that no system is completely secure can encourage more thoughtful decisions about what digital content to create and how to store it.
The Path Forward
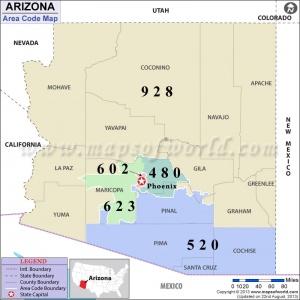
The nude photos scandal exploding in the 520 area code and similar incidents across the country represent a critical moment in our relationship with digital technology. As we become increasingly connected and our lives more digitized, the stakes for privacy violations continue to rise. The question is no longer whether someone can access our private information, but rather how we can create systems that respect privacy while acknowledging the reality of digital vulnerability.
The solution likely involves a combination of better technology, stronger laws, cultural change around consent and privacy, and individual awareness about digital security. Until these elements align, scandals like the one unfolding in the 520 area code will continue to remind us of the fragility of digital privacy in an interconnected world.
Conclusion
The nude photos scandal exploding in the 520 area code is more than just another privacy violation; it's a symptom of a larger problem in our digital society. From the 2014 celebrity leaks that shocked the world to the organized exploitation networks uncovered by police, we've seen how intimate content can be weaponized against individuals for profit, revenge, or entertainment.
As technology continues to evolve and our lives become increasingly digitized, the importance of robust privacy protections cannot be overstated. The victims of these scandals—whether celebrities, political figures, or ordinary people—deserve better than to have their most private moments exposed to the world. Until we create systems that truly respect and protect digital privacy, we must all remain vigilant about the content we create, the platforms we trust, and the potential consequences of living in an always-connected world.