770 Area Code Scandal: How Your Phone Number Is Being Leaked For Sex!
Have you ever wondered why you're suddenly receiving suspicious texts, calls, or messages from unknown numbers? If you're in Georgia's 770 area code, you might be experiencing a disturbing trend that's affecting thousands of residents. The 770 area code scandal has emerged as a major privacy concern, with phone numbers being leaked and exploited for inappropriate purposes. But how did this happen, and what can you do to protect yourself?
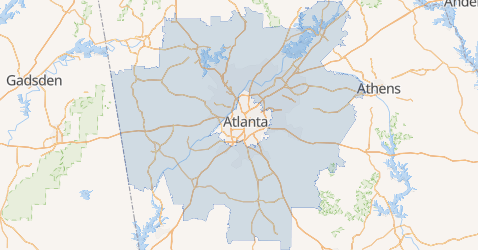
The 770 area code covers a significant portion of Georgia, including major cities like Marietta, Roswell, and Alpharetta. This area code was established in 1995 as a split from the original 404 area code, and it now serves millions of residents and businesses. However, recent reports indicate that phone numbers within this region are being harvested from various databases and sold on the dark web, leading to a surge in harassment, scam attempts, and exploitation.
Understanding the 770 Area Code and the Current Situation
Area code 770 belongs to Georgia, United States, covering the suburban areas north of Atlanta. This area code was created to accommodate the growing population and demand for new phone numbers in the Atlanta metropolitan area. However, what was once just a geographic designation has now become associated with a troubling trend of phone number leaks.
- Christopher Plummers Secret Sex Tapes From Tv Shows Leaked Fans Are Outraged
- The One Tea That Destroys Sore Throats In Minutes Shocking Discovery
- You Wont Believe Belles Secret In This Leaked Disney Porn Clip
The 770 area code scandal involves multiple layers of privacy violations. First, phone numbers are being scraped from public records, social media platforms, and data breaches. Second, these numbers are being compiled into lists that are sold to various entities, including those with malicious intent. Third, the leaked numbers are being used for everything from telemarketing spam to more serious criminal activities.
The scale of this problem is significant. According to cybersecurity experts, Georgia has seen a 45% increase in phone-based harassment cases over the past year, with the 770 area code being disproportionately affected. This suggests that the region is being targeted specifically, possibly due to the demographic makeup of the area or the availability of data.
What You Need to Do Immediately
Here's what you need to do if you suspect your phone number has been compromised. Time is of the essence when dealing with phone number leaks, as the longer you wait, the more damage can be done to your privacy and security.
- The Nude Truth About Baby Teething What They Dont Want You To See
- Exclusive Leak Ames Movies 12 Theaters Secret Adult Screenings Exposed
- The Heartbreaking Leak Alexander Goulds Secret Struggle After Finding Nemo
First, contact your mobile service provider to let them know your number has been compromised and that someone has been illegally accessing your accounts. Most major carriers have dedicated fraud departments that can help you secure your account. They may recommend changing your number, adding additional security measures, or monitoring your account for suspicious activity.
When you contact your provider, be prepared to provide specific details about the suspicious activity you've noticed. This might include unknown charges on your bill, unusual texts or calls, or notifications about account changes you didn't make. The more information you can provide, the better they can assist you in securing your account.
Second, enable two-factor authentication (2FA) on all your accounts that offer it. This adds an extra layer of security that makes it much harder for someone to access your accounts even if they have your phone number. Consider using an authenticator app rather than SMS-based 2FA, as SMS can be intercepted if someone has control of your number.
Securing Your Accounts with Alternative Verification Methods
You can use either a safe phone number or an authenticator app to protect your accounts. Traditional SMS verification has become increasingly vulnerable as phone numbers are leaked and compromised. Fortunately, there are more secure alternatives available.
A safe phone number service provides you with a secondary number that you can use for verification purposes without exposing your primary number. These services often include additional privacy features and can be canceled or changed if they become compromised. Some popular options include Google Voice, Burner, and various other virtual phone number services.
Authenticator apps like Google Authenticator, Authy, or Microsoft Authenticator generate time-based one-time passwords (TOTP) that are much more secure than SMS codes. These apps don't rely on your phone number at all, making them immune to SIM swapping attacks and other methods that exploit phone number vulnerabilities. They work even when you don't have cellular service, providing both security and convenience.
Is Your Phone Number Leaked Online?
Worried your phone number leaked online? You're not alone in this concern. With the increasing number of data breaches and the growing sophistication of cybercriminals, phone number leaks have become alarmingly common. The question is no longer if your information has been leaked, but rather what information has been leaked and how you can protect yourself.
Several online tools can help you determine if your phone number appears in data breaches. Websites like Have I Been Pwned allow you to check if your email or phone number has been involved in known data breaches. While these tools aren't comprehensive, they can give you an idea of whether your information is circulating online.
Additionally, you can use search engines to look for your phone number. Simply type your number into quotation marks in the search bar to see if it appears on any websites. You might be surprised to find your number listed on people-search websites, public records databases, or even social media profiles. Each of these instances represents a potential vulnerability that could be exploited by bad actors.
Understanding the Risks and Protecting Your Privacy
Learning how to check, what risks it creates, and the steps to protect your privacy, accounts, and identity is crucial in today's digital landscape. When your phone number is leaked, it opens the door to a range of potential threats that can affect every aspect of your digital life.
The risks of a leaked phone number are extensive. Identity thieves can use your number to reset passwords on your accounts, intercept two-factor authentication codes, and gain access to your financial information. Scammers can use your number for phishing attempts, pretending to be from legitimate organizations to trick you into revealing sensitive information. Harassers can use your number to send threatening or inappropriate messages, causing emotional distress and potentially escalating to more serious forms of harassment.
Moreover, leaked phone numbers can lead to SIM swapping attacks, where criminals convince your mobile carrier to transfer your number to a SIM card they control. Once they have control of your number, they can receive all your calls and texts, including verification codes for banking and other sensitive services. This type of attack has become increasingly common and can result in significant financial losses and identity theft.
Snapchat and Social Media Privacy Concerns
How to check if your snapchat account info was leaked or wonder if your username or phone number was included in the snapchat leak? Social media platforms have become a major source of phone number leaks, often through data breaches or through features designed to help users connect with friends.
Snapchat experienced a significant data breach in 2023 where millions of users' phone numbers were exposed. If you're a Snapchat user in the 770 area code, you might be particularly concerned about whether your information was part of this leak. The platform has since implemented additional security measures, but the damage from the initial breach cannot be undone.
A simple tool will help you find out if your Snapchat information was compromised. The Snapchat Data Leak Checker allows you to input your username or phone number to see if it was part of any known breaches. This tool cross-references your information against databases of leaked credentials and can provide you with information about whether your data was exposed and what specific information was leaked.
Beyond Snapchat, other social media platforms have also experienced similar issues. Facebook, Instagram, and Twitter have all had data breaches that exposed user phone numbers. Additionally, features like "Find Friends" that allow you to connect with people who have your phone number can inadvertently expose your information to more people than you intended.
Comprehensive Protection Strategies
Protecting yourself from phone number leaks requires a multi-faceted approach. Start by auditing your online presence and removing your phone number from any unnecessary public listings. This includes social media profiles, online directories, and any websites where you might have listed your contact information.
Next, consider using a secondary phone number for non-essential services. Many businesses and websites require a phone number for registration, but they don't need your primary number. Using a virtual number or a secondary SIM card for these purposes can help contain potential damage if that information is leaked.
Be cautious about sharing your phone number online. Before entering your number on any website or app, consider whether it's truly necessary. Many services that request your phone number can function without it, or they may offer alternative verification methods. When in doubt, use a temporary or virtual number instead.
Regularly monitor your accounts for suspicious activity. This includes checking your bank statements, credit reports, and account login histories. Many services offer activity notifications that can alert you to unusual login attempts or changes to your account settings. These early warning systems can help you catch and respond to potential security breaches before they cause significant damage.
The Role of Mobile Carriers and Data Brokers
Understanding how phone numbers end up leaked requires examining the role of mobile carriers and data brokers. Mobile carriers collect vast amounts of data about their customers, including call logs, text message metadata, and location information. While this data collection is often justified for billing and service improvement purposes, it creates significant privacy vulnerabilities.
Data brokers aggregate information from multiple sources, including public records, social media, and data breaches, to create detailed profiles of individuals. These profiles often include phone numbers, addresses, and other personal information that can be purchased by anyone willing to pay. The data broker industry operates with minimal regulation in many jurisdictions, creating a Wild West environment where personal information is bought and sold without the knowledge or consent of the individuals involved.
Some mobile carriers have been criticized for their data sharing practices, with reports of customer information being sold to third parties or being poorly secured against breaches. While many carriers have improved their security measures in response to public pressure, the fundamental business model of collecting and monetizing customer data remains a concern for privacy advocates.
Legal and Regulatory Considerations
The legal landscape surrounding phone number privacy is complex and varies by jurisdiction. In the United States, there is no comprehensive federal law protecting phone number privacy, though various sector-specific regulations provide some protections. The Telephone Consumer Protection Act (TCPA) regulates telemarketing calls and texts but doesn't prevent the initial collection and sharing of phone numbers.
Some states have enacted stronger privacy protections. California's Consumer Privacy Act (CCPA) gives residents the right to know what personal information is being collected about them and to request that it be deleted. However, enforcement of these laws is often inconsistent, and many companies continue to collect and share phone numbers without explicit consent.
The European Union's General Data Protection Regulation (GDPR) provides stronger protections for personal data, including phone numbers, but these protections only apply to EU residents and companies operating in the EU. For most Americans, the legal protections for phone number privacy remain limited, making individual vigilance and proactive security measures essential.
Conclusion: Taking Control of Your Phone Number Privacy
The 770 area code scandal is just one example of a broader problem affecting phone users across the country. As our phone numbers become increasingly tied to our digital identities, protecting them from leaks and exploitation becomes more critical than ever. By understanding the risks, taking proactive security measures, and staying informed about potential breaches, you can significantly reduce your vulnerability to phone number-related privacy violations.
Remember that protecting your phone number is an ongoing process, not a one-time fix. Regularly review your security settings, monitor your accounts for suspicious activity, and be cautious about where and how you share your phone number. Consider using alternative verification methods like authenticator apps, and don't hesitate to contact your mobile carrier if you suspect your number has been compromised.
The digital age has brought unprecedented convenience and connectivity, but it has also created new vulnerabilities that we must actively work to protect against. By taking control of your phone number privacy and implementing the strategies outlined in this article, you can enjoy the benefits of modern communication without falling victim to the growing threats of phone number exploitation and identity theft.